Hey there, tech enthusiasts! If you’re into AI development or cybersecurity, you’ve probably heard about the latest buzz surrounding a critical vulnerability. On June 30, 2025, security researcher Avi Lum dropped a bombshell on X about a zero-day flaw in Anthropic’s MCP Inspector, labeled as CVE-2025-49596. This isn’t just another tech glitch—it’s a Remote Code Execution (RCE) vulnerability that could let attackers run arbitrary bash commands on your system just by visiting a malicious website. Let’s break it down in simple terms and figure out what it means for you.
What’s the MCP Inspector, Anyway?
The MCP Inspector is a handy tool from Anthropic, designed to help developers evaluate and debug projects using the Model Context Protocol (MCP). It’s widely used across the industry, even by big names like Google, OpenAI, and Microsoft, because it’s the go-to method for running MCP projects locally. Think of it as a trusted assistant that starts a proxy server on your machine to analyze your work. But here’s the catch: that trust was misplaced until recently.
The Vulnerability Exposed
Avi’s discovery revealed a gaping hole. The MCP Inspector’s local server, which runs by default when you use commands like mcp dev or npx @modelcontextprotocol/inspector, had no authentication and accepted any bash commands as arguments. Worse, it bound to 0.0.0.0, a sneaky IP address that can be exploited by any webpage through a technique called a “#0000 trick.” Imagine this: you’re browsing the web, stumble upon a shady site, and boom—attackers can execute code on your machine without you lifting a finger.
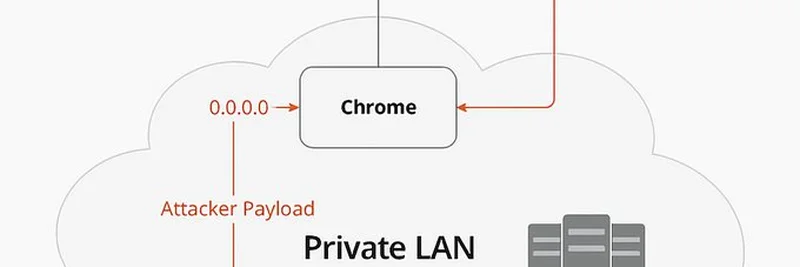
The diagram below, shared by Avi, paints a clear picture of how this works:
Here’s the flow:
- An attacker’s website (
attacker.com) sends a payload via a GET request. - Your Chrome browser, acting as the middleman, forwards this to the
0.0.0.0address. - The payload slips into your Private LAN, hitting the MCP Inspector process.
- From there, it can potentially reach MCP servers, giving attackers a foothold.
Scary stuff, right? This vulnerability earned a Critical CVSS score of 9.4, signaling a serious threat.
Who’s at Risk?
If you’re an AI developer using the MCP Inspector in its default setup, you’re a potential target. The tool’s popularity means many projects—especially those relying on open-source MCP servers—are exposed. Even casual users running it for debugging could be hit, making this a widespread concern.
The Fix Is Here
Good news! Anthropic and the community acted fast. The latest version, MCP Inspector v0.14.1, patches this flaw. It locks down the local server, adds command validation, and includes DNS rebinding protection to block those pesky 0.0.0.0 exploits. To stay safe, update your global NPM instance with npm install -g and ensure each project uses the new version. Avi also noted that some MCP Inspector instances were exposed online, so checking your setup is a smart move—more details are in the full research blog.
Why This Matters for Blockchain and Meme Token Fans
You might wonder, “What’s this got to do with meme tokens or blockchain?” Well, as the lines between AI and blockchain blur—think AI-driven smart contracts or decentralized AI projects—this vulnerability could impact the security of those ecosystems. At Meme Insider, we’re all about keeping you informed, and this is a reminder to stay vigilant. A compromised tool could lead to hacked wallets or manipulated token launches, so securing your dev environment is key.
Final Thoughts
Kudos to Avi Lum and Anthropic for tackling this head-on. It’s a great example of how open-source projects can respond to threats with speed and professionalism. If you’re using MCP Inspector, update now and keep an eye on your configurations. For the latest tech news and security tips tailored to blockchain enthusiasts, stick with us at Meme Insider. Got questions? Drop them in the comments—we’re here to help!